Proton VPN Complete Guide 2026
A comprehensive, privacy-first guide designed for users who want complete control over their digital identity. Learn how Proton VPN protects your data, bypasses surveillance, and secures your internet activity in 2026 and beyond.
The Internet Privacy Crisis in 2026
The modern internet has evolved into a complex ecosystem where personal data is constantly collected, analyzed, and monetized. Internet service providers monitor traffic, websites deploy aggressive tracking systems, advertisers build behavioral profiles, and governments expand digital surveillance capabilities.
In 2026, privacy threats are no longer limited to obvious risks like public Wi-Fi hacking. Today’s dangers include invisible tracking pixels, metadata harvesting, DNS monitoring, deep packet inspection, and cross-platform fingerprinting. Even users who believe they have nothing to hide are affected by these practices.
Proton VPN exists to counter these threats by restoring the fundamental right to privacy. It does so by encrypting your internet traffic, masking your real IP address, and preventing third parties from identifying, profiling, or tracking your online behavior.
Why Proton VPN Is Different
Many VPN services focus primarily on entertainment features such as streaming access or aggressive marketing claims. Proton VPN takes a fundamentally different approach. It is built by privacy engineers and scientists with the goal of defending digital freedom rather than exploiting user data.
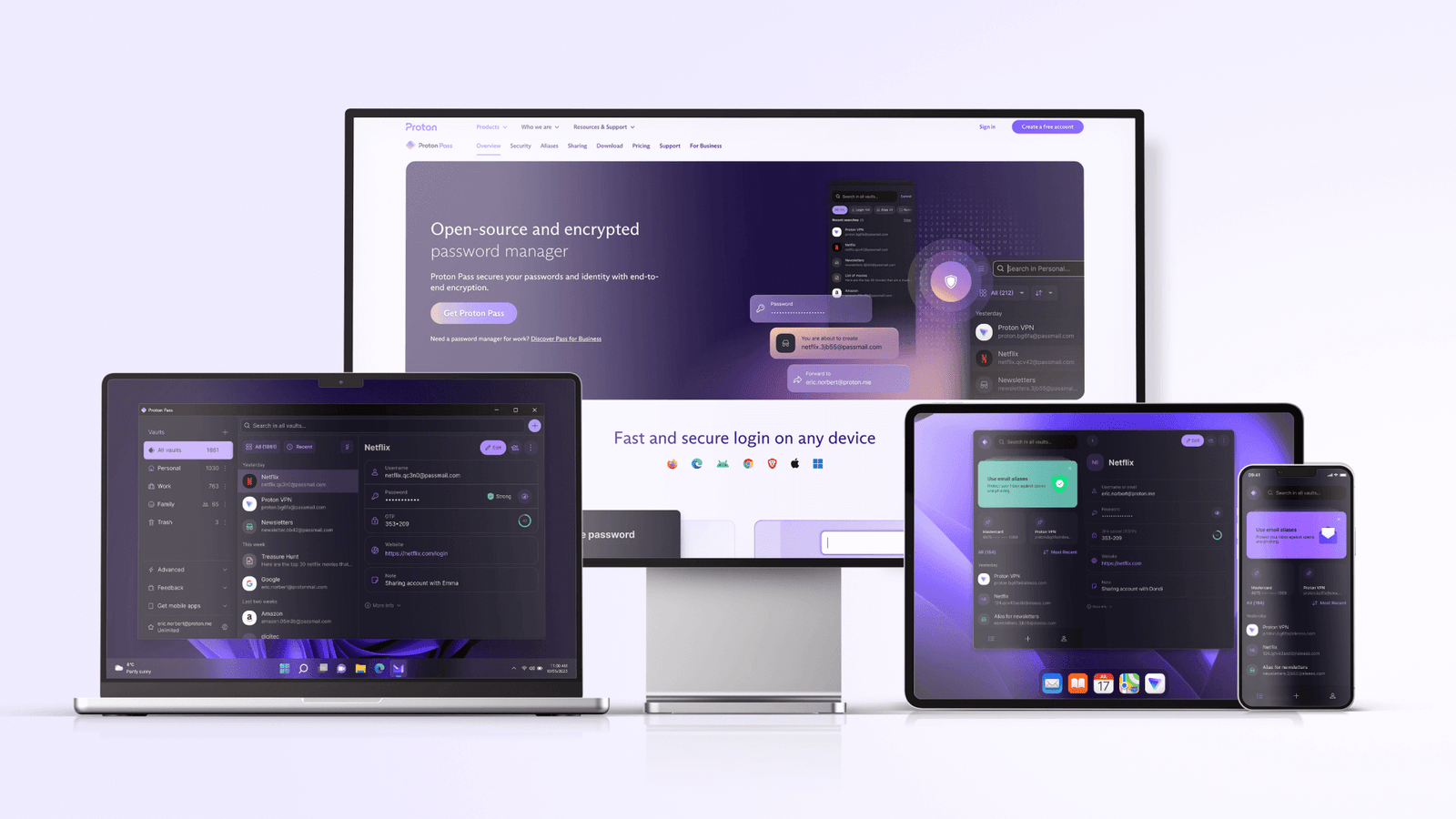
Proton VPN is developed as part of a broader privacy ecosystem that prioritizes transparency, ethical design, and long-term user trust. Instead of collecting analytics or selling anonymized data, Proton VPN minimizes data exposure at every level of its architecture.
What Is Proton VPN?
Proton VPN is a virtual private network service that creates a secure, encrypted tunnel between your device and the internet. This tunnel prevents third parties from seeing what you do online and hides your real location by replacing your IP address with one from a VPN server.
Unlike standard internet connections where data travels openly through your ISP’s infrastructure, a VPN connection ensures that your traffic remains confidential from the moment it leaves your device until it reaches its destination.
Proton VPN is designed for users who want both simplicity and advanced protection. Beginners can connect with a single click, while advanced users can fine-tune protocols, routing methods, and security layers.
How Proton VPN Works – A Simple Explanation
When you connect to Proton VPN, your device establishes a secure connection to a VPN server operated by Proton. All internet traffic passing through this connection is encrypted before it leaves your device.
Encryption ensures that even if someone intercepts your data, it appears as unreadable code rather than usable information. Your internet service provider can see that data is being transmitted, but it cannot see the content, destination, or purpose of that data.
At the same time, websites and online services no longer see your real IP address. Instead, they see the IP address of the VPN server, which protects your real location and identity.
The Security Foundation Behind Proton VPN
Strong Encryption by Design
Proton VPN uses modern encryption standards designed to withstand both current and future threats. Encryption keys are generated securely, exchanged safely, and rotated regularly to prevent long-term exposure.
Perfect Forward Secrecy
Each VPN session uses unique encryption keys. This means that even if one session were somehow compromised, previous and future sessions would remain protected.
Secure Authentication
Proton VPN verifies both the client and the server during connection establishment, preventing man-in-the-middle attacks and unauthorized server impersonation.
Strict No-Logs Policy
Proton VPN is built on a strict no-logs philosophy. This means it does not record browsing activity, connection timestamps, bandwidth usage, or IP addresses that could identify users.
By collecting as little data as possible, Proton VPN ensures there is nothing meaningful to hand over even under legal pressure. User privacy is protected by design rather than promises.
Who This Guide Is For
This guide is written for anyone who wants to understand Proton VPN at a deeper level. Whether you are a beginner seeking basic protection or an advanced user interested in privacy engineering, this guide provides practical and technical insights.
In the next sections, we will explore Proton VPN’s advanced features, real-world use cases, performance optimization, and expert-level configuration strategies.
Advanced Proton VPN Features Explained
Proton VPN is engineered with multiple layers of protection that work together to secure user traffic. These features are not marketing add-ons but core components of the VPN’s privacy architecture.
Modern Encryption Standards
Proton VPN encrypts data using strong cryptographic algorithms designed to resist brute-force attacks and future computational threats.
Secure VPN Protocols
Users can choose protocols optimized for speed, reliability, or censorship resistance depending on their environment.
Kill Switch Protection
If the VPN connection drops unexpectedly, all internet traffic is immediately blocked to prevent data exposure.
NetShield Filtering
Network-level blocking stops ads, trackers, and malicious domains before they ever reach your device.
Secure Core Architecture
Secure Core is Proton VPN’s most advanced privacy feature. Instead of connecting directly to a VPN server, traffic is routed through multiple secure locations before exiting to the public internet.
This design protects users from traffic correlation attacks and server compromise. Even if an exit server were monitored, attackers would not be able to trace traffic back to the user.
Secure Core is especially valuable for journalists, activists, and users operating in high-risk regions.
Real-World Use Cases
Remote Work & Business
Proton VPN secures business data, protects cloud access, and prevents network interception on home or public networks.
Travel & Public Wi-Fi
Travelers rely on Proton VPN to avoid rogue hotspots, hotel Wi-Fi attacks, and location-based restrictions.
High-Privacy Scenarios
Secure Core and no-logs architecture provide advanced anonymity for sensitive research and communication.
Performance & Speed Optimization
Proton VPN balances privacy with performance through intelligent routing and optimized protocols. While encryption adds overhead, proper configuration minimizes speed loss.
- Use nearby servers for lower latency
- Select WireGuard for daily browsing
- Avoid Secure Core when speed is critical
- Enable VPN accelerator features
Frequently Asked Questions
Secure Your Digital Freedom
Proton VPN is more than a VPN—it is a long-term privacy solution. Take control of your data, protect your identity, and browse with confidence in 2026.